
The Difference Between CTFs and AppSec
1. Real Applications Are Vastly More Complex CTFs typically involve hunting for vulnerabilities in custom-built applications designed specifically for the challenge. These apps are intentionally[…]

A Guide to AWS S3 Bucket Penetration Testing
Introduction Misconfigurations in cloud environments and resulting data breaches frequently put AWS Simple Storage Service in the news. In “Hands-On AWS Penetration Testing with Kali[…]

A Complete Guide To ISO 27001 Penetration Testing
Introduction ISO 27001 compliance entails proving that an organization’s information security management system (ISMS) aligns with the standard’s requirements. Achieving compliance requires undergoing an audit[…]
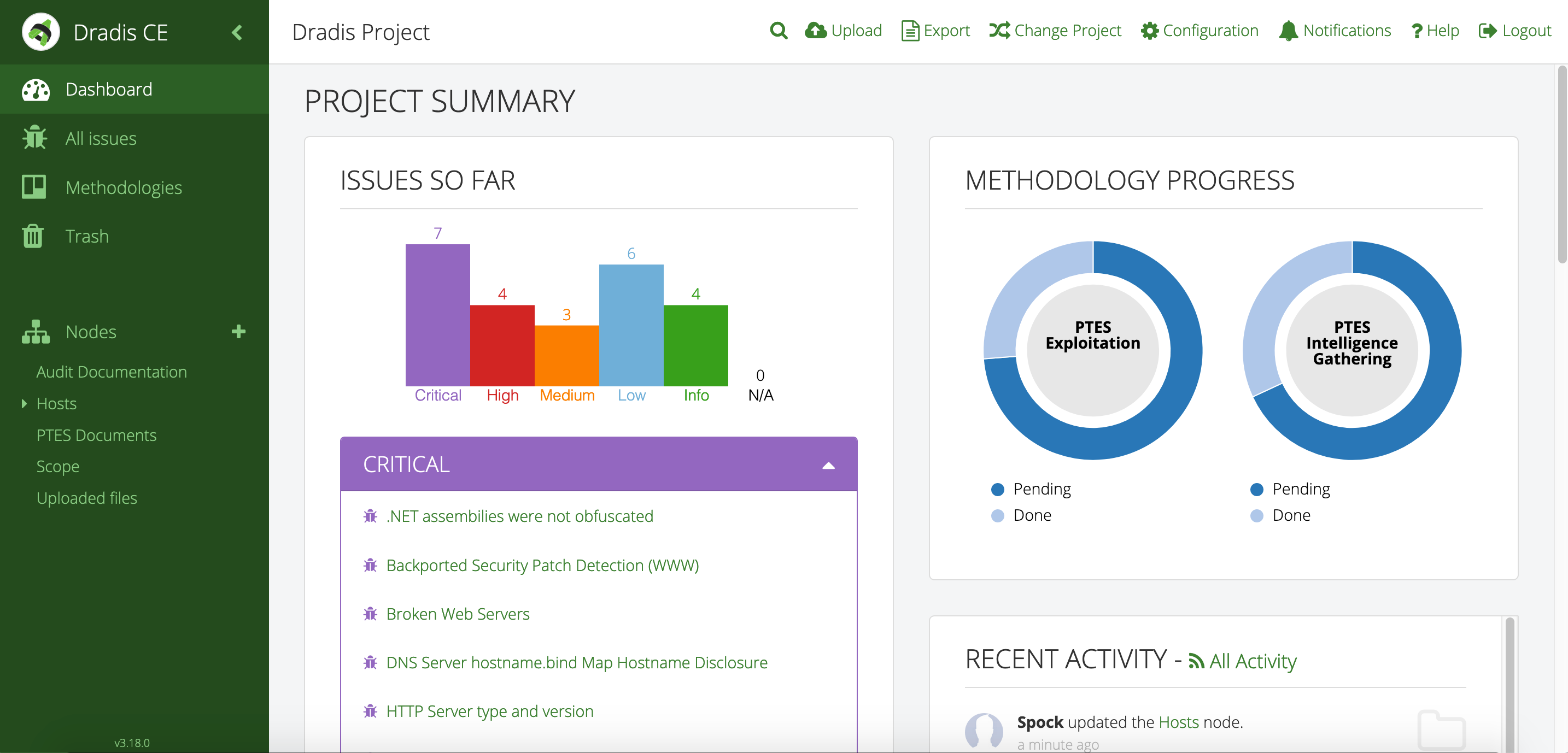
An Introduction to Report Generating With Dradis
Introduction As cyber security professionals traverse the complex landscape of security assessments and penetration tests, smooth reporting and collaboration are critical for success. One tool that has gained[…]

A Penetration Testing Compliance Guide
Introduction In many cases, penetration testing – an ethical engagement designed for identification and addressing of security vulnerabilities in systems, applications and networks, is required. Sometimes[…]

A Major Insurance Company Refused to Pay Hackers a Ransom for a Major Data Breach, Here’s What Happened Next
Between February 7th and March 7th 2023, hackers were able to breach over the personal information of almost 9 million individuals in the United States[…]

The Most Dangerous Cyber Security Threat in Medellin, Colombia
In today’s interconnected world, cyber security has become paramount. As our reliance on digital technology grows, so too do the threats posed by cyber criminals.[…]

How an Old Server Increased a Company’s Attack Surface and Lead to a Major Data Breach
Zacks Investment Research Data, a major stock market data research provider, revealed a major breach in their network allowing attackers to expose 820,000 individual’s data.[…]

How the MOVEit Vulnerability Punctured Numerous Government Agencies
In May 2023, a managed file transfer program named MOVEit, used by a wide range of private businesses and government agencies experienced major data breach[…]

The TMX Breach and the Importance of Endpoint Protections
TMX Finance, parent company of TitleMax, TitleBucks and InstaLoan experienced a major breach of their network, resulting in nearly 5 million customer accounts’ data being[…]


